Abruptly returning to a previous topic, here’s a guest dispatch from Famicoman (AKA Mike Dank) on surveillance and privacy. Back to the new focus soon.
The letter sat innocently in a pile of mail on the kitchen table. A boring envelope, nondescript at a glance, that would become something of a Schrödinger’s cat before the inevitable unsealing. The front of it bared the name of the sender, in bright, black letters — “U.S. Department of Justice — Federal Bureau of Investigations.” This probably isn’t something that most people would ever want to find in their mailbox.
For me, the FBI still conjures up imagery straight out of movies, like the bumbling group in 1995’s Hackers, wrongfully pursuing Dade Murphy and his ragtag team of techno-misfits instead of the more sinister Plague. While this reference is dated, I still feel like there is a certain stigma placed upon the FBI, especially by the technophiles who understand there is more to computing than web browsers and document editing. As laws surrounding computers become more sophisticated, we can see them turn draconian. Pioneers, visionaries, and otherwise independent thinkers can be reduced to little more than a prisoner number.
Weeks earlier, I had submitted a Privacy Act inquiry through the FBI’s Freedom of Information Act service. For years, the FBI and other three-letter-agencies have allowed people to openly request information on a myriad of subjects. I was never particularly curious about the outcome of a specific court case or what information The New York Times has requested for articles; my interests were a bit more selfish.
Using the FBI’s eFOIA portal through their website, I filled out a few fields and requested my own FBI file. Creating a FOIA request is greatly simplified these days, and you can even use free services, such as getmyfbifile.com, to generate forms that can be sent to different agencies. I only opted to pursue the FBI at this time, but could always query other agencies in the future.
The whole online eFOIA process was painless, taking maybe two minutes to complete, but I had hesitations as my cursor hovered over the final “Submit” button. Whether or not I actually went through with this, I knew that the state of the information the FBI had on me already wouldn’t falter. They either have something, or they don’t, and I think I’m ready to find out. With this rationalization, I decided to submit — in more ways than one.
The following days went by slowly and my mind seemed to race. I had read anecdotes from people who had requested their FBI file, and knew the results could leave me with more questions than answers. I read one account of someone receiving a document with many redactions, large swathes of blacked-out text, giving a minute-by-minute report of his activities with a collegiate political group. A few more accounts mentioned documents of fully-redacted text, pages upon pages of black lines and nothing else.
What was I in store for? It truly astonishes me that a requester would get back anything at all, even a simple acknowledgement that some record exists. In today’s society where almost everyone has a concern about their privacy, or at least an acknowledgement that they are likely being monitored in some way, the fact that I could send a basic request for information about myself seems like a nonsensical loophole in our current cyberpolitical climate. You would never see this bureaucratic process highlighted in the latest technothriller.
About two weeks after my initial request, there I was, staring at the letter sticking out from the mail stack on the kitchen table. All at once, it filled me with both gloom and solace. This was it, I was going to see what it spelled out, for better or worse. Until I opened it, the contents would remain both good and bad news. After slicing the envelope, I unfolded the two crisp pieces of paper inside, complete with FBI letterhead and a signature from the Record/Information Dissemination Section Chief. As I ingested the first paragraph, I found the line that I hoped I would, “We were unable to identify main records responsive to the FOIA.”
Relief washed over, and any images I had of suited men arriving in black vans to take me away subsided (back down to the normal levels of paranoia, at least). It was the best information I could have received, but not at all what I had expected. For over ten years, I have been involved in several offbeat Internet subcultures and groups, and more than a few sound reason enough to land me on someone’s radar. I was involved with a popular Internet-based hacking video show, held a role in a physical hacking group/meeting, hosted a Tor relay, experimented openly with alternative, secure mesh networks, sysop’d a BitTorrent tracker, and a few other nefarious things here and there.
I always tried to stay on the legal side of things, but that doesn’t mean that I don’t dabble with technologies that could be used for less than savory purposes. In some cases, just figuring out how something can be done was more rewarding than the thought of using it to commit an act or an exploit. Normal people (like friends and coworkers) might call me “suspicious” or tell me I was “likely on a list,” but I didn’t seem to be from what I could gather from the response in front of me.
When I turned back to read the second paragraph, I eyed an interesting passage, “By standard FBI practice and pursuant to FOIA exemption… and Privacy Act exemption… this response neither confirms or denies the existence of your subject’s name on any watch lists.” So maybe I was right to be worried. Maybe I am being watched. I would have no way of knowing. This “neither confirms or denies” response is called a Glomar, which means my information has the potential to be withheld as a matter of national security, or over privacy concerns.
Maybe they do have information on me after all. Even if I received a flat confirmation that there is nothing on me, would I believe it? What is to prevent a government organization from lying to me for “my own good”? How can I be expected to show any semblance of trust at face value? Now that all is said and done, I don’t know much more than I did when I started, and have little to show for the whole exchange besides an official request number and a few pieces of paper with boilerplate, cover-your-ass language.
If we look back at someone like Kevin Mitnick, the cunning social engineer who received a fateful knock on his hotel door right before being arrested in early 1995, we see a prime example of law enforcement pursuing someone not only for the actions they took, but the skills and knowledge they possess. Echoing Operation Sundevil, only five years prior, government agencies wanted to make examples out of their targets, and incite scare tactics to keep others in line.
I can’t help but think of “The Hacker Manifesto,” written by The Mentor (an alias used by Loyd Blankenship) in 1986. “We explore… and you call us criminals. We seek knowledge… and you call us criminals,” Blankenship writes shortly after being arrested himself. Even if I received a page of blacked-out text in the mail, would I be scared and change my habits? What if I awoke to a hammering on my door in the middle of the night? I still don’t know what to make of my response, but maybe I’ll submit another request again next year.
Knock, knock.
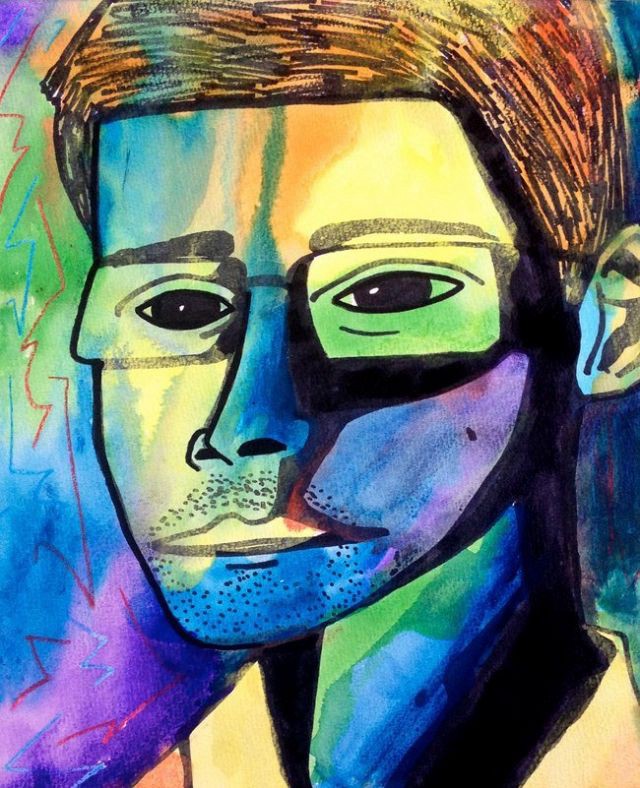
Header artwork by Matt Brown.